Key Concepts
There are 5 basic processes: Registration, KYC, New Device Authorization, Recovery, Authentication.
Registration
Basic registration requires only phone verification. After successful registration Identity asset and Device asset bind to Identity are created and a user can continue with the next steps.
KYC(Know Your Customer)
During the KYC procedure, a user provides images of identification documents and selfie(Document Verification), his address with images containing proof of this address(Address Verification) and, optionally, email address.
New Device Authorization
User can bind multiple devices to his Identity. To do so user sends DeviceAuthorization Request and approves it from any authorized Device. Device goes to a list of authorized devices and gets all permissions. User can manage list of devices by removing devices.
Recovery
When a user lost access to all his authorized devices and wants to recover access to his account(Identity). He has to pass the same steps, passed during the registration, to recover access to his Identity. On successful recovery request, all previous Devices will be removed from Identity and replaced with the current Device.
Authentication
Any verified method provided during registration and KYC can be used as additional(in addition to authentification by private key) authentification method to authorize financial transactions known as Strong Customer Authentification(SCA), to open new working session after logout, to change critical user preferences.
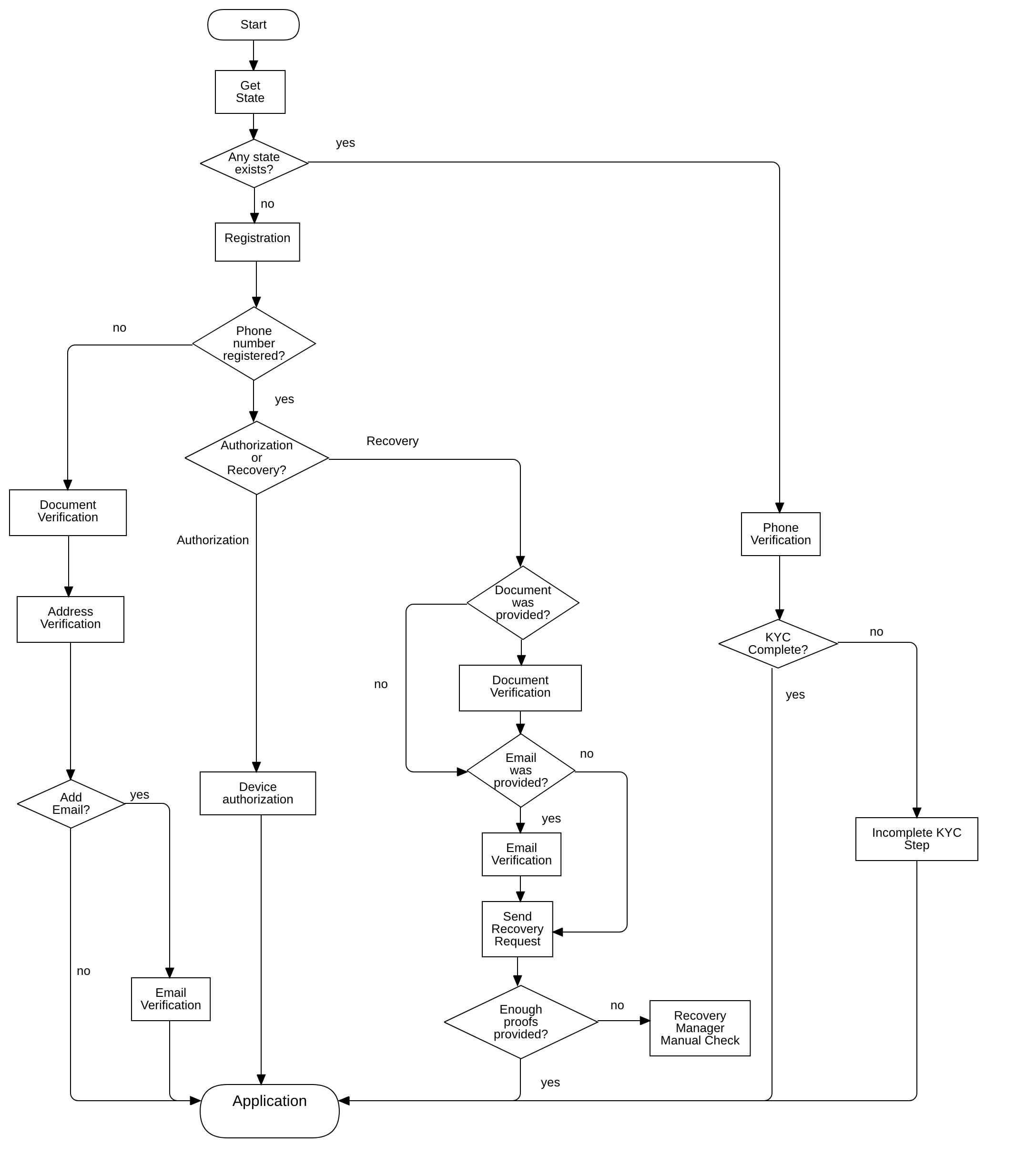
Flow Chart
The diagram below should help you better understand the processes of KYC module. And buld your application based on Omniwire SDK. Some bullet points:
- When application starts and SDK is initialized you need to call getState to check whether the device was registered or not.
- If the device was already registered you need to redirect the user to the login page or directly to uncompleted KYC stage.
- If the device doesn’t have any state we ask the user for a phone number registration
- If the phone number has not been registered in the system user is redirected to the beginning of the KYC procedure.
- If the phone number is registered in the system user has two options: New Device Authorization or Recovery